Want to give codebreaking a shot?
When we read this book by Jason Fagone about Elizebeth Smith Friedman’s work codebreaking, we were quickly bitten by the cryptology bug. Months later, that inspiration manifested into The Cryptology Collections, a collection of pattern designs inspired by code. What about you? Do you want to give codebreaking a shot?
Before you get started, let’s define a few codebreaking & building terms.
Cryptology: the scientific study of cryptography and cryptanalysis
Code: a system of symbols (such as letters or numbers) used to represent assigned and often secret meanings
Cipher: a method of transforming a text in order to conceal its meaning; a message in code
For The Cryptology Collections, we used traditional ciphers to build our designs. In addition, we created a few of our own ciphers too. If you’d like to give codebreaking a shot and figure out the messages in our patterns, here are the ciphers you need in order to crack the code.
Traditional Ciphers
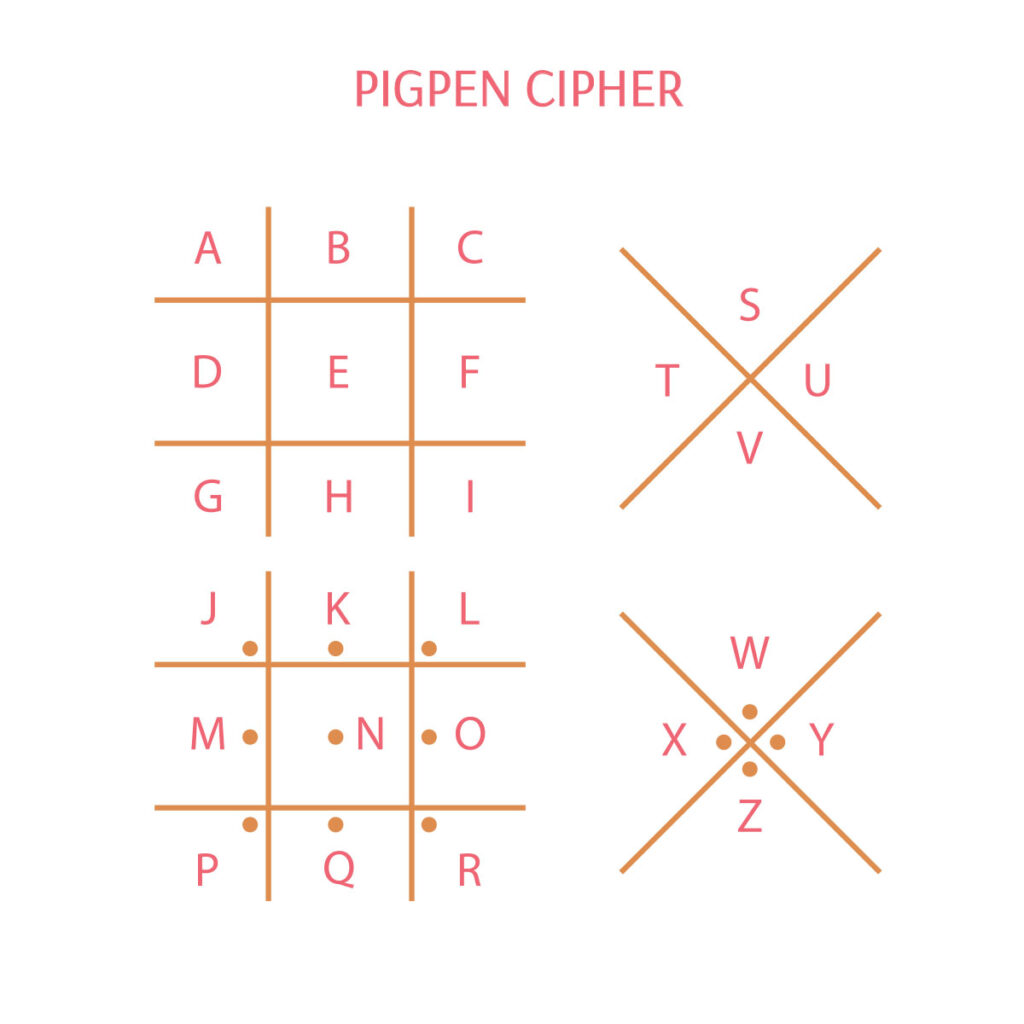
Pigpen Cipher
The Pigpen Cipher is one of the oldest ciphers. It is a geometric simple substitution cipher where letters are exchanged for symbols, which are fragments of a grid.
We used a pigpen cipher for pattern Encode (P1912a).
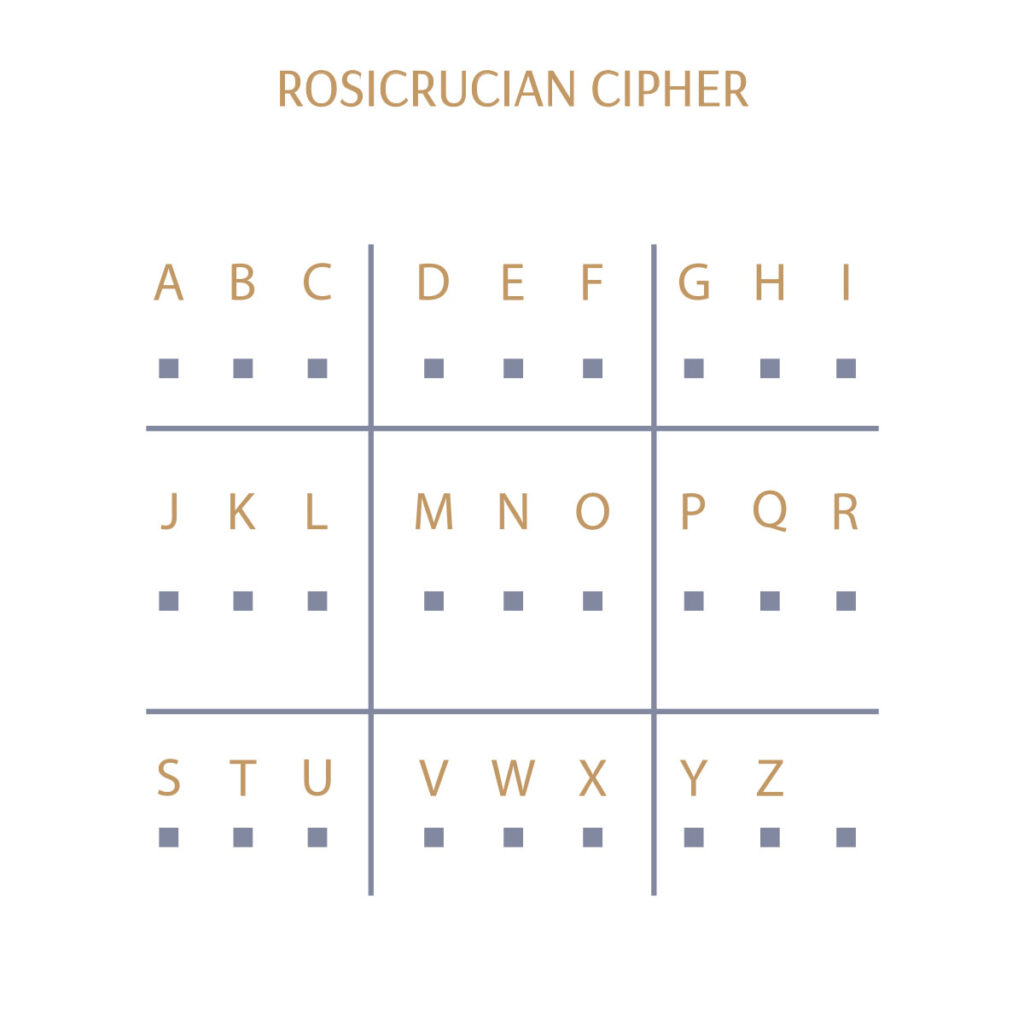
Rosicrucian Cipher
The Rosicrucian Cipher is a variation of a pigpen cipher and was used by the Rosicrucian brotherhood.
We used this cipher in patterns Pen to Paper (P1899) and Key (P1911a).
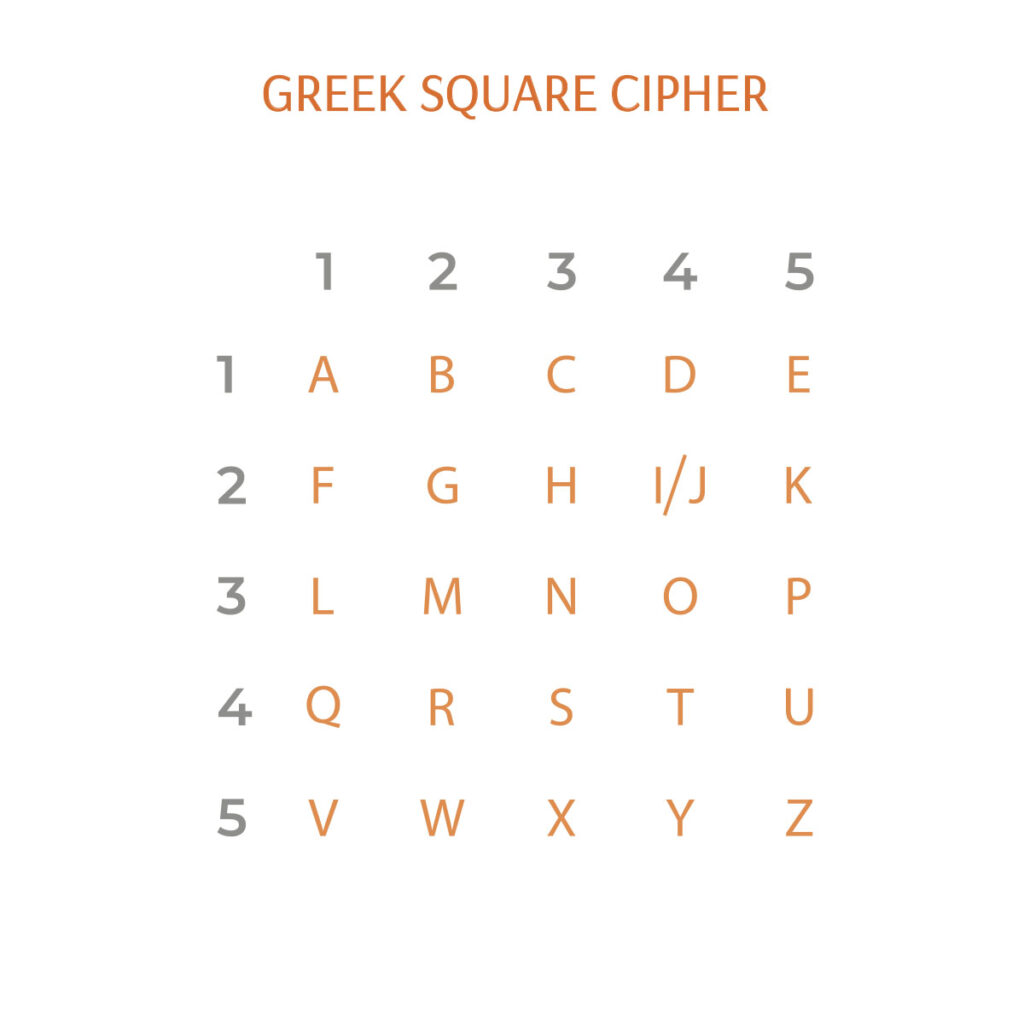
Greek Square Cipher
A Greek Square Cipher was used by the ancient Greeks and worked well for their 25 character alphabet. In order for this cipher to work with our 26 letter alphabet, the I and J are combined.
We used the Greek Square Cipher in pattern Daisy Chain (P1906a).
Bar Code Cipher
A Bar Code Cipher exchanges letters for a combination of two different size stripes.
We used a bar code cipher in patterns Bird (P1904a), Traffic (P1918a), Riverbank (P1903a), and Code (P1909a).

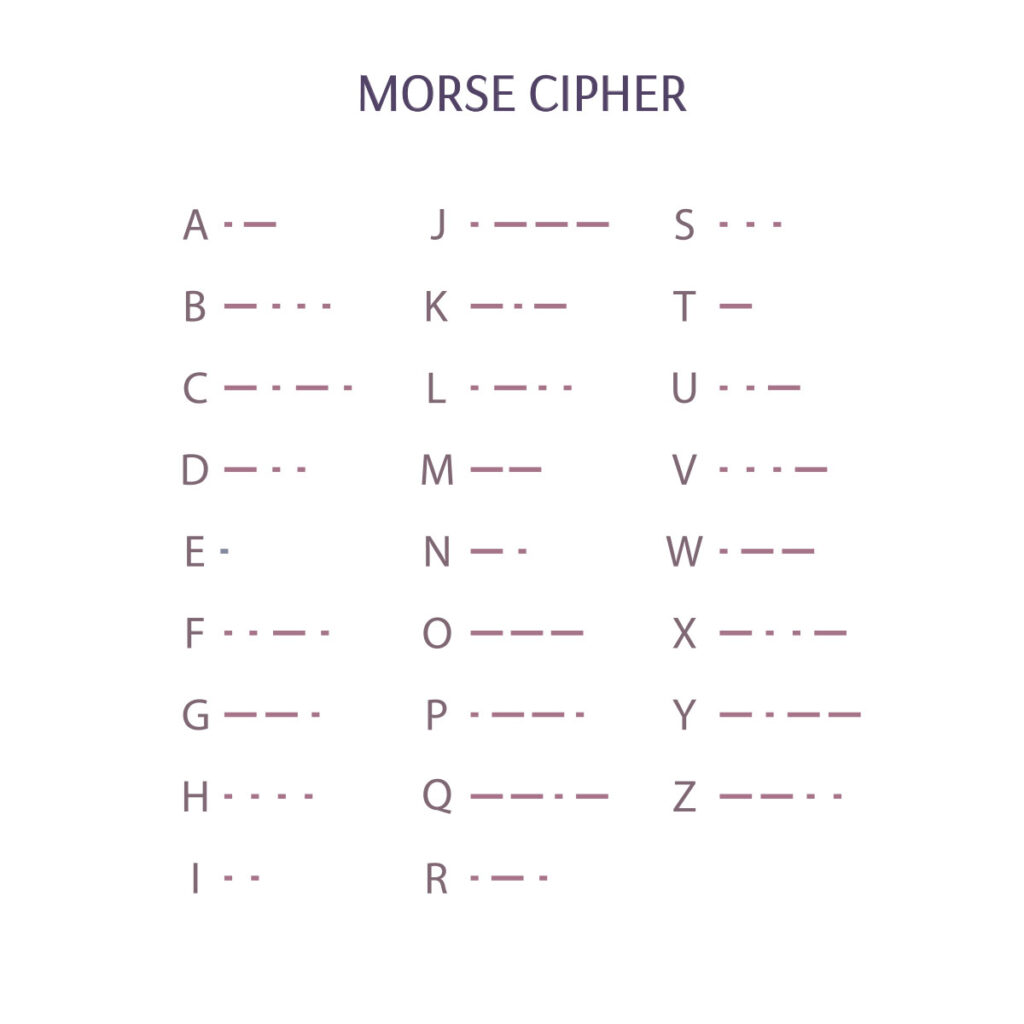
Morse Code Cipher
Morse Code uses dots and dashes to correspond to different letters to communicate a message.
We used a More Code Cipher on patterns Decipher (P1913a), Ciphertext (P1910a), Folio (P1900a), Message (P1916a), Sanguine P1924a, Science (P1908a), and Letters P1925a
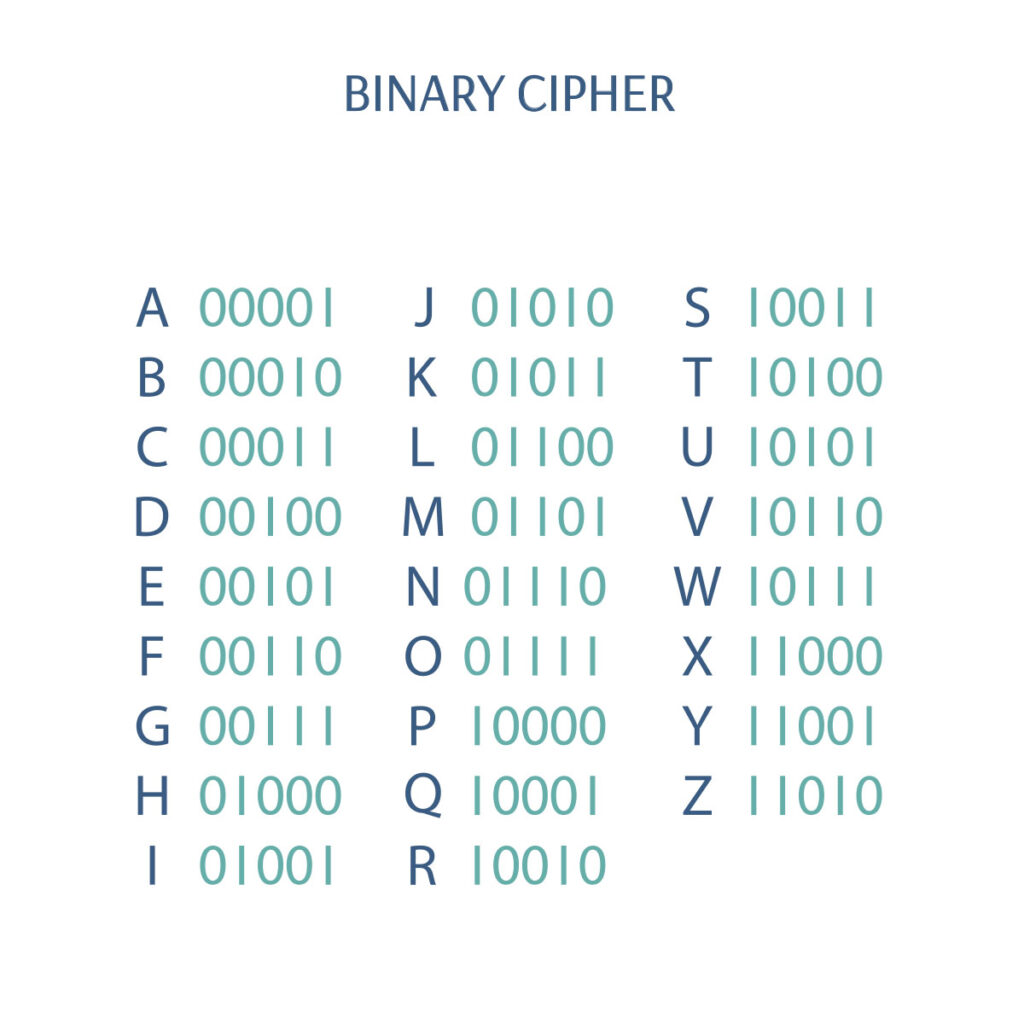
Binary Code Cipher
Binary code uses combinations of “0” and “1” to correspond to letters.
We used a Binary Code Cipher on patterns Railroad (P1907a), Five Languages (P1905a), Telegraph (P1917a), and Signals (P1915a),
Design Pool Ciphers
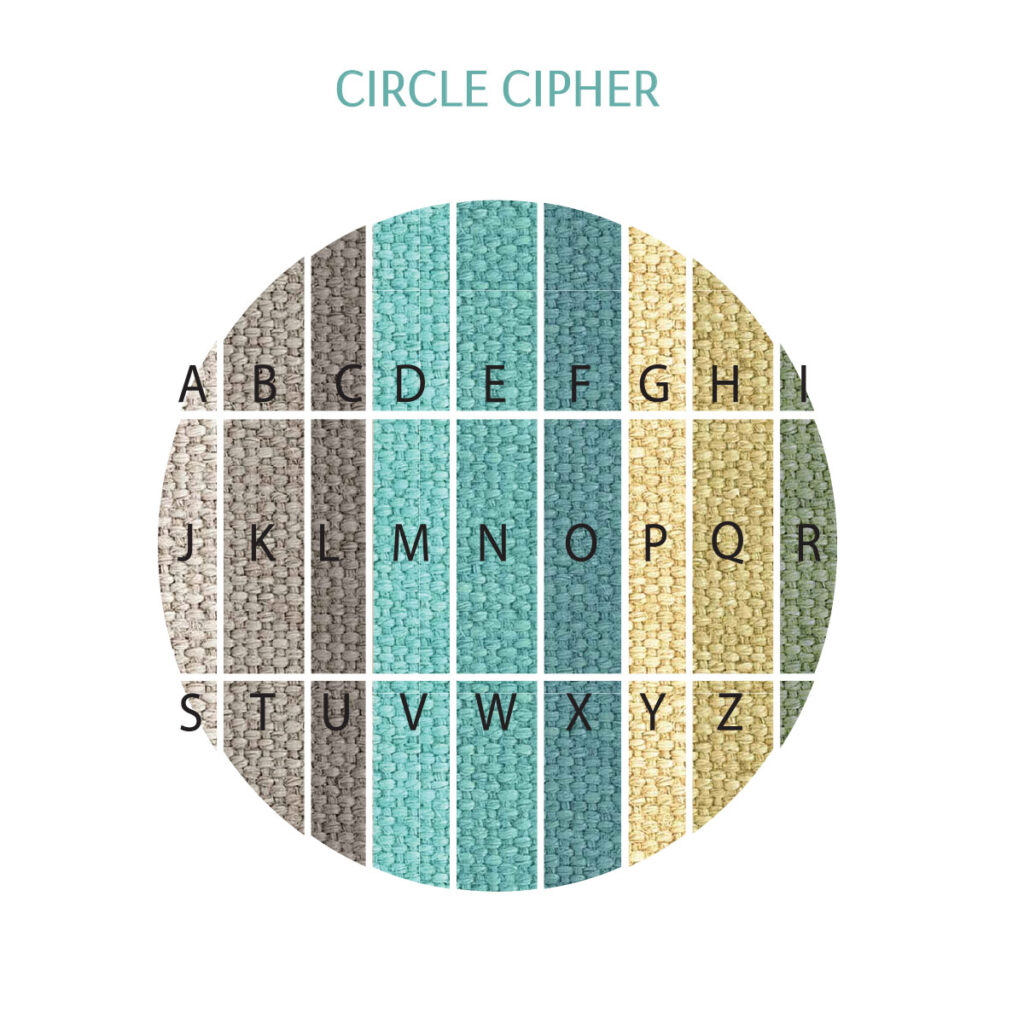
Inspired by ciphers, we made a few of our own for this collection. We developed three different ciphers based on circles.
Circle Cipher
This cipher is based on the idea of the Rosicrucian Cipher. Using a circle, we divided it with a grid and used color to identify each letter of the alphabet.
We used our Circle Cipher on patterns In Depth (P1902a), Frequency (P1901a), and Tujjedy (P1914a).
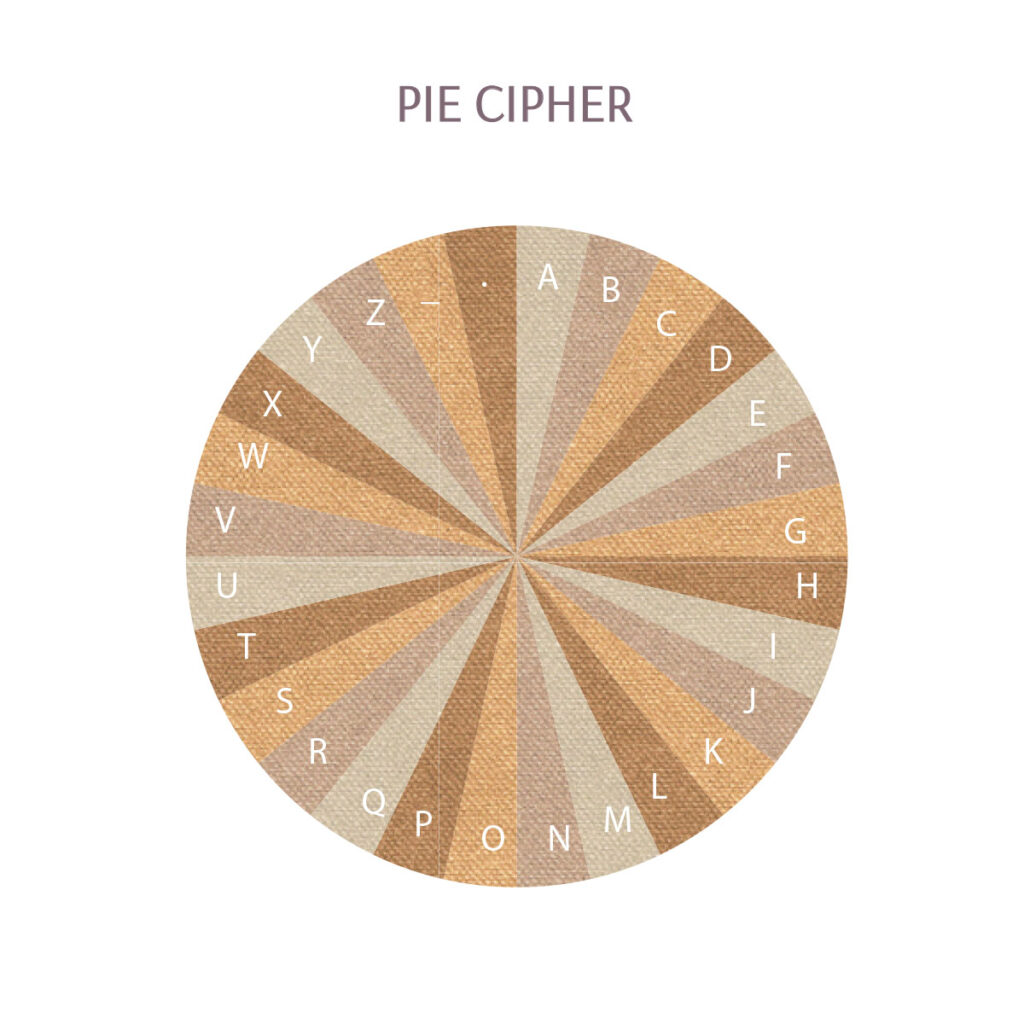
Pie Cipher
This cipher uses a circle divided like a pie chart into 26 equal parts. Then we use color and pie slice placement to identify the letters.
We used this on pattern Dance (P1927a).
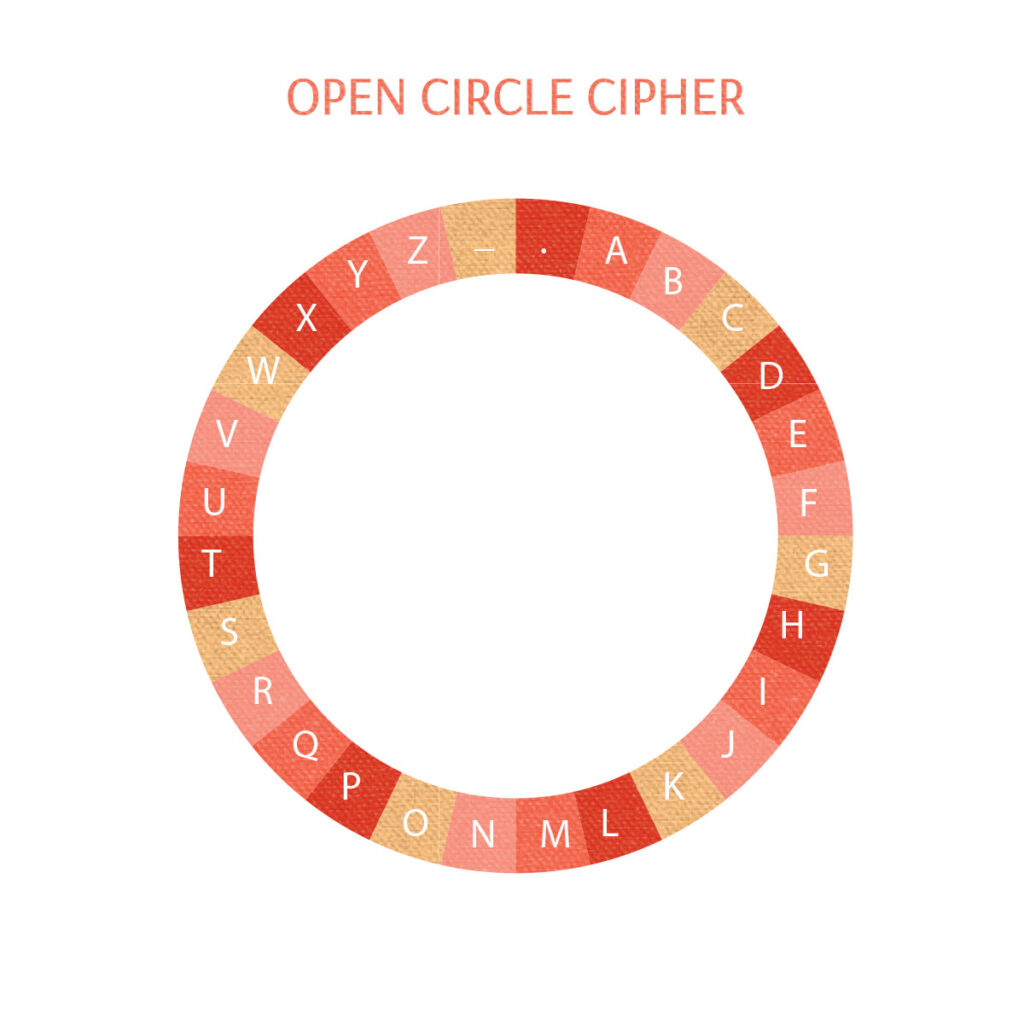
Open Circle Cipher
This is similar to our Pie Cipher but is missing the inside of the circle.
We used this on pattern Spindrift (P1923a) and Playful (P1922a).
If learning about Elizebeth Smith Friedman and codebreaking is inspiring you, we hope you’ll take a crack at deciphering some of the messages in the designs of our Cryptology Collections. If you’ll be at NeoCon, let us know you cracked the codes. We’ll enter all correct answers into a drawing for a chance to win a Cryptology prize pack! We’ll announce the winner on Instagram, so be sure you’re following us.
Be sure to visit us in Booth 7-4049 on the 7th floor of the MART.
Share this post
Author
DESIGN/COLOR TRENDS AND AWESOME INFORMATION IN YOUR INBOX
Sign up for our monthly trend letter